
Double Security for Online Services
Dieser Artikel ist älter als ein Jahr!
Why is e-banking secure? In addition to the encryption of the data traffic between your computer and the bank, there is a second layer of security. If someone gets your user name and password, they still can`t complete transfers because they also need a TAN code to do this. And these are no longer printed on a piece of paper, but are sent on demand by text message. More and more web services are now also offering the same service. This can be enabled and disabled in the account security settings for Google, Facebook and Dropbox.
Two-channel authenticationYou need two things to log in: something that you know (your user name and password) and something you have (your mobile phone). This way, another person who knows your user name and password still cannot log in.
The increasing prevalence of account theft shows why this is important. The hack in the
, the
hack and the theft of
passwords are just a few examples of the many incidents. Dropbox recently sent an e-mail to its users offering "two-step authentication" and asked them to provide a mobile phone number.
The conventional login method is especially vulnerable when the same user name and password are used for multiple services. Anyone who knows the password can access many services at the same time.
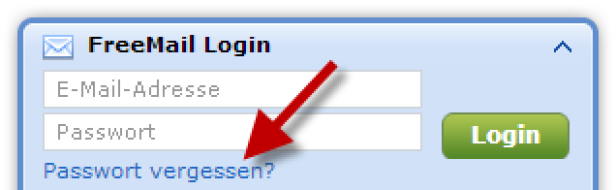
Security is especially critical for mail services. Even if you use different passwords for all of your services, an attacker who has access to your e-mail can use the forgotten password function that many services offer to have a password sent by e-mail, and can then change all the other access information. Some providers even allow you to access an e-mail account after you answer a few security questions for which the answers are easy to find.
© Georg Holzer
The case of Wired editor
, whose complete digital life was cracked by answering a few security questions, shows how easy social engineering – obtaining access credentials with the help of sites like Wikipedia – really is.
And with computing power growing as fast as it is, even the most complex passwords are potentially unsafe.
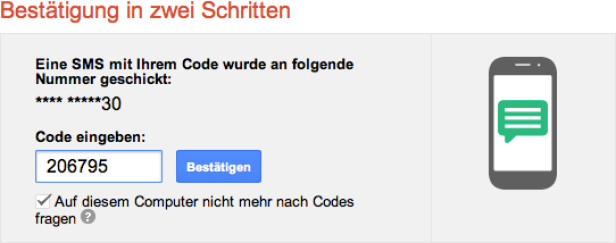
How it worksWhen two-factor authentication is enabled, a six-character code is sent by text message after you enter your user name and password. You cannot access your account until this code has been entered.
© Georg Holzer
That means that a third person who knows your user name and password also needs to have access to your mobile phone. So you are reliably protected against a hacker in China or a jealous boyfriend or girlfriend. But this does not mean that you can use passwords like "jenny1980".
Trusted computersBecause the login process is somewhat more complicated, you can define specific devices such as your smartphone, iPad, work computer or home computer as "trusted." Then, you will not have to enter a security code for a certain period of time. How long this is varies from provider to provider.
Two-step confirmation at GoogleFor Google, "2-step verification" can be turned on in your account settings under Security. But the Internet company is not consistent, and the secure authentication method is not available for all Google services.
There are "application-specific passwords" for all services that are not yet supported (such as Google Reader and Google Talk). These are secure passwords that are only valid for one specific service.
If you do not like receiving login text messages, you can also download the authenticator app for iOS, Android, Windows Phone or Blackberry (installation through the mobile web site m.google.com/authenticator). The app calculates the random codes that are otherwise sent by text message every minute. Google offers programming interfaces for other web sites for the authenticator app, so this system has become the de facto standard.
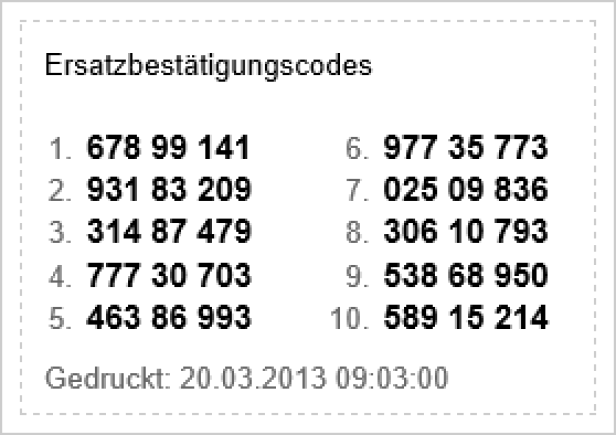
But what happens when you lose your mobile phone or don`t have it with you? There are backup codes for such an instance that you can obtain from the security page in your account settings and that you should print out.
© Georg Holzer
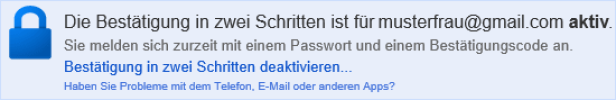
If the double security system is too complicated, you can disable it at any time. The settings for this can be found in the light blue bar above the security settings.
© Georg Holzer
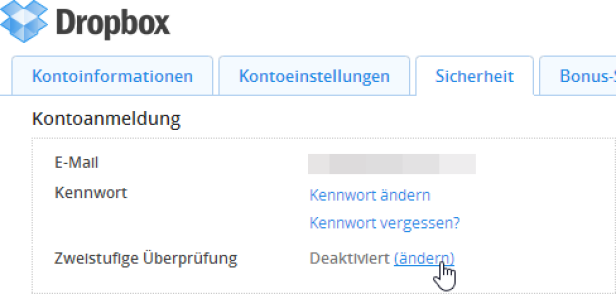
Two-step verification for DropboxThe cloud storage service Dropbox is one of the most sensitive services because it is often used to save and synchronize important and personal data. This makes it all the more important that you enable double protection for your account.
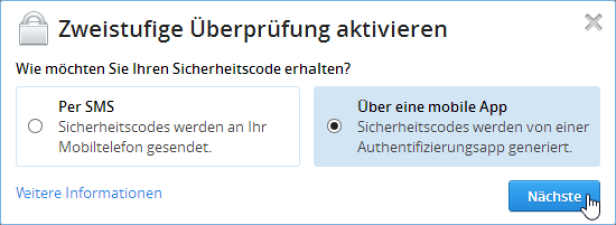
© Georg Holzer
"Two-step verification" can be found in the security settings. Click the "change" link to configure the settings. It only takes a few seconds.
© Georg Holzer
You can receive the security codes for Dropbox by text message or through Google`s Authenticator app (see above). A QR code is used to configure the Authenticator app, as is the case with Google.
Login approvals for FacebookFacebook only offers the option of a double login by text message.
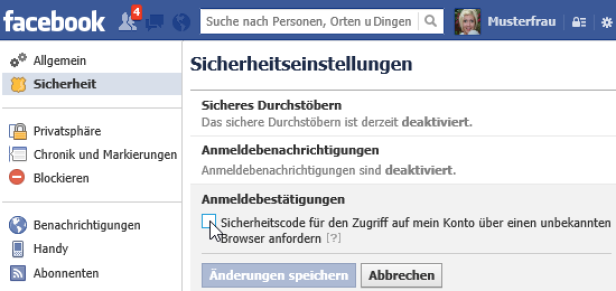
© Georg Holzer
You can enable login approvals in the security settings. Here as well, you do not have to constantly authenticate yourself on your home computer. You will only receive a code from time to time.
Two-step verification at AppleIt has taken Apple a good eight months since a high-profile case of
to start rolling out its "two-step verification" at the end of March.
When it is available, the settings will be found on the pages for managing your Apple ID under "Password and Security."
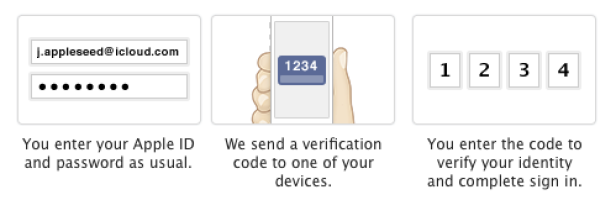
© Georg Holzer
Apple uses text messages and the Find iPhone app as a second level of security.
Google Authenticator for your own web siteAnyone who runs their own web site is also interested in ensuring that no unauthorized persons can log in. A practical plugin for the content management system WordPress also allows the Authenticator app from Google to be used for access control.
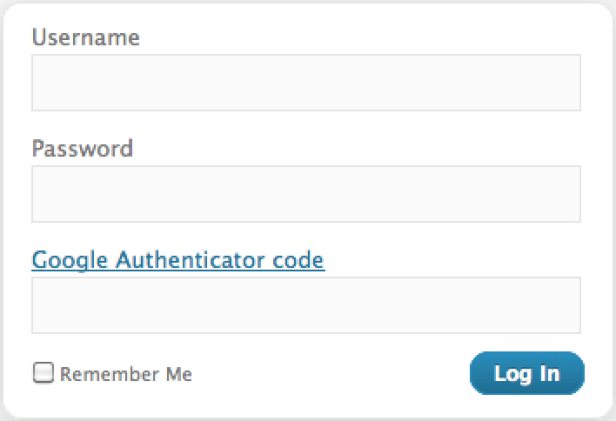
© Georg Holzer
Such extensions are also available for Typo3 and Drupal.
Further providersPayPal calls this login method Security Key, and Amazon Web Services offers multi-factor authentication. The Evernote note service is still working on its two-factor authentication. The online password manager LastPass uses the Google Authenticator, as does the hosting provider Dreamhost. Administrators can also secure Windows computers with a password (something you know) and smart cards (something you have).
Kommentare